When A User Makes Changes To The Settings Of A Windows System, Where Are These Changes Stored?
| | |
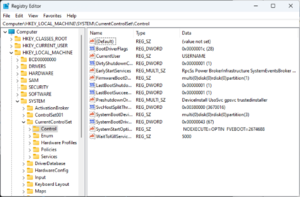 Registry Editor, the user interface for the registry, in Windows ten | |
| Developer(s) | Microsoft |
|---|---|
| Initial release | April half dozen, 1992 (1992-04-06) with Windows three.i |
| Operating system | Microsoft Windows |
| Platform | IA-32, x86-64 and ARM (and historically DEC Blastoff, Itanium, MIPS, and PowerPC) |
| Included with | Microsoft Windows |
| Type | Hierarchical database |
| Website | docs |
The Windows Registry is a hierarchical database that stores low-level settings for the Microsoft Windows operating system and for applications that opt to use the registry. The kernel, device drivers, services, Security Accounts Director, and user interfaces can all employ the registry. The registry also allows access to counters for profiling system performance.
In other words, the registry or Windows Registry contains information, settings, options, and other values for programs and hardware installed on all versions of Microsoft Windows operating systems. For example, when a program is installed, a new subkey containing settings such as a plan's location, its version, and how to offset the program, are all added to the Windows Registry.
When introduced with Windows 3.one, the Windows Registry primarily stored configuration information for COM-based components. Windows 95 and Windows NT extended its utilize to rationalize and centralize the information in the profusion of INI files, which held the configurations for individual programs, and were stored at various locations.[i] [2] It is not a requirement for Windows applications to apply the Windows Registry. For example, .Net Framework applications use XML files for configuration, while portable applications usually proceed their configuration files with their executables.
Rationale [edit]
Prior to the Windows Registry, .INI files stored each program's settings equally a text file or binary file, oftentimes located in a shared location that did not provide user-specific settings in a multi-user scenario. Past contrast, the Windows Registry stores all awarding settings in one logical repository (but a number of discrete files) and in a standardized form. According to Microsoft, this offers several advantages over .INI files.[2] [3] Since file parsing is done much more efficiently with a binary format, it may be read from or written to more chop-chop than a text INI file. Furthermore, strongly typed data tin be stored in the registry, as opposed to the text information stored in .INI files. This is a do good when editing keys manually using regedit.exe, the congenital-in Windows Registry Editor. Because user-based registry settings are loaded from a user-specific path rather than from a read-only system location, the registry allows multiple users to share the same machine, and besides allows programs to piece of work for less privileged users. Fill-in and restoration is also simplified as the registry tin be accessed over a network connection for remote management/support, including from scripts, using the standard set up of APIs, as long as the Remote Registry service is running and firewall rules permit this.
Because the registry is a database, it offers improved arrangement integrity with features such every bit atomic updates. If 2 processes attempt to update the same registry value at the same time, one process'southward modify will precede the other'due south and the overall consistency of the data will be maintained. Where changes are made to .INI files, such race conditions can result in inconsistent information that does non match either attempted update. Windows Vista and later on operating systems provide transactional updates to the registry by means of the Kernel Transaction Managing director, extending the atomicity guarantees beyond multiple central and/or value changes, with traditional commit–abort semantics. (Annotation still that NTFS provides such back up for the file system as well, so the same guarantees could, in theory, exist obtained with traditional configuration files.)
Structure [edit]
Keys and values [edit]
The registry contains two basic elements: keys and values. Registry keys are container objects similar to folders. Registry values are non-container objects similar to files. Keys may incorporate values and subkeys. Keys are referenced with a syntax similar to Windows' path names, using backslashes to betoken levels of hierarchy. Keys must have a case insensitive proper noun without backslashes.
The hierarchy of registry keys can only be accessed from a known root central handle (which is anonymous but whose effective value is a abiding numeric handle) that is mapped to the content of a registry key preloaded by the kernel from a stored "hive", or to the content of a subkey within some other root key, or mapped to a registered service or DLL that provides access to its contained subkeys and values.
E.one thousand. HKEY_LOCAL_MACHINE\Software\Microsoft\Windows refers to the subkey "Windows" of the subkey "Microsoft" of the subkey "Software" of the HKEY_LOCAL_MACHINE root central.
In that location are vii predefined root keys, traditionally named co-ordinate to their constant handles defined in the Win32 API, or past synonymous abbreviations (depending on applications):[4]
- HKEY_LOCAL_MACHINE or HKLM
- HKEY_CURRENT_CONFIG or HKCC
- HKEY_CLASSES_ROOT or HKCR
- HKEY_CURRENT_USER or HKCU
- HKEY_USERS or HKU
- HKEY_PERFORMANCE_DATA (only in Windows NT, but invisible in the Windows Registry Editor)[5]
- HKEY_DYN_DATA (only in Windows 9x, and visible in the Windows Registry Editor)
Similar other files and services in Windows, all registry keys may be restricted by admission control lists (ACLs), depending on user privileges, or on security tokens acquired by applications, or on organization security policies enforced by the organization (these restrictions may be predefined past the system itself, and configured by local arrangement administrators or past domain administrators). Unlike users, programs, services or remote systems may only see some parts of the hierarchy or distinct hierarchies from the same root keys.
Registry values are proper name/data pairs stored inside keys. Registry values are referenced separately from registry keys. Each registry value stored in a registry key has a unique proper noun whose letter of the alphabet case is non significant. The Windows API functions that query and manipulate registry values take value names separately from the central path and/or handle that identifies the parent key. Registry values may contain backslashes in their names, but doing so makes them hard to distinguish from their key paths when using some legacy Windows Registry API functions (whose usage is deprecated in Win32).
The terminology is somewhat misleading, every bit each registry key is similar to an associative array, where standard terminology would refer to the name part of each registry value as a "cardinal". The terms are a holdout from the 16-bit registry in Windows three, in which registry keys could not contain capricious proper noun/data pairs, simply rather contained only i unnamed value (which had to be a string). In this sense, the Windows three registry was like a single associative array, in which the keys (in the sense of both 'registry primal' and 'associative array key') formed a hierarchy, and the registry values were all strings. When the 32-bit registry was created, so was the additional capability of creating multiple named values per key, and the meanings of the names were somewhat distorted.[6] For compatibility with the previous behavior, each registry key may take a "default" value, whose name is the empty string.
Each value can store arbitrary data with variable length and encoding, merely which is associated with a symbolic type (defined as a numeric abiding) defining how to parse this data. The standard types are:[7]
| Type ID | Symbolic blazon name | Pregnant and encoding of the data stored in the registry value |
|---|---|---|
| 0 | REG_NONE | No type (the stored value, if whatsoever) |
| i | REG_SZ | A string value, ordinarily stored and exposed in UTF-16LE (when using the Unicode version of Win32 API functions), commonly terminated by a NUL graphic symbol |
| two | REG_EXPAND_SZ | An "expandable" string value that can contain environment variables, normally stored and exposed in UTF-16LE, ordinarily terminated by a NUL character |
| iii | REG_BINARY | Binary information (any arbitrary data) |
| 4 | REG_DWORD / REG_DWORD_LITTLE_ENDIAN | A DWORD value, a 32-bit unsigned integer (numbers between 0 and 4,294,967,295 [ii32 – ane]) (little-endian) |
| 5 | REG_DWORD_BIG_ENDIAN | A DWORD value, a 32-bit unsigned integer (numbers betwixt 0 and four,294,967,295 [two32 – 1]) (large-endian) |
| 6 | REG_LINK | A symbolic link (UNICODE) to another registry key, specifying a root fundamental and the path to the target key |
| seven | REG_MULTI_SZ | A multi-string value, which is an ordered listing of not-empty strings, usually stored and exposed in Unicode, each one terminated past a nothing character, the listing being normally terminated past a second null character.[8] |
| 8 | REG_RESOURCE_LIST | A resource listing (used by the Plug-n-Play hardware enumeration and configuration) |
| 9 | REG_FULL_RESOURCE_DESCRIPTOR | A resource descriptor (used by the Plug-north-Play hardware enumeration and configuration) |
| 10 | REG_RESOURCE_REQUIREMENTS_LIST | A resource requirements list (used by the Plug-n-Play hardware enumeration and configuration) |
| 11 | REG_QWORD / REG_QWORD_LITTLE_ENDIAN | A QWORD value, a 64-bit integer (either large- or little-endian, or unspecified) (introduced in Windows 2000)[nine] |
Root keys [edit]
The keys at the root level of the hierarchical database are by and large named by their Windows API definitions, which all begin "HKEY".[2] They are often abbreviated to a three- or iv-letter short name starting with "HK" (due east.g. HKCU and HKLM). Technically, they are predefined handles (with known constant values) to specific keys that are either maintained in memory, or stored in hive files stored in the local filesystem and loaded by the system kernel at boot time and then shared (with various access rights) between all processes running on the local arrangement, or loaded and mapped in all processes started in a user session when the user logs on the organisation.
The HKEY_LOCAL_MACHINE (local machine-specific configuration data) and HKEY_CURRENT_USER (user-specific configuration information) nodes have a similar structure to each other; user applications typically look up their settings by first checking for them in "HKEY_CURRENT_USER\Software\Vendor's name\Application's name\Version\Setting proper noun", and if the setting is not plant, await instead in the same location under the HKEY_LOCAL_MACHINE central[ citation needed ]. However, the converse may apply for administrator-enforced policy settings where HKLM may take precedence over HKCU. The Windows Logo Program has specific requirements for where different types of user data may be stored, and that the concept of least privilege be followed and then that ambassador-level access is not required to use an awarding.[a] [x]
HKEY_LOCAL_MACHINE (HKLM) [edit]
Abbreviated HKLM, HKEY_LOCAL_MACHINE stores settings that are specific to the local figurer.[11]
The key located past HKLM is actually not stored on disk, but maintained in retentivity by the system kernel in order to map all the other subkeys. Applications cannot create any additional subkeys. On Windows NT, this fundamental contains iv subkeys, "SAM", "SECURITY", "SYSTEM", and "SOFTWARE", that are loaded at boot fourth dimension inside their corresponding files located in the %SystemRoot%\System32\config folder. A fifth subkey, "HARDWARE", is volatile and is created dynamically, and as such is not stored in a file (it exposes a view of all the currently detected Plug-and-Play devices). On Windows Vista and to a higher place, a sixth and 7th subkey, "COMPONENTS" and "BCD", are mapped in memory by the kernel on-demand and loaded from %SystemRoot%\system32\config\COMPONENTS or from boot configuration data, \boot\BCD on the system partitioning.
- The "HKLM\SAM" key usually appears as empty for most users (unless they are granted access by administrators of the local arrangement or administrators of domains managing the local organization). Information technology is used to reference all "Security Accounts Director" (SAM) databases for all domains into which the local system has been administratively authorized or configured (including the local domain of the running system, whose SAM database is stored in a subkey likewise named "SAM": other subkeys will be created as needed, one for each supplementary domain). Each SAM database contains all builtin accounts (by and large group aliases) and configured accounts (users, groups and their aliases, including invitee accounts and administrator accounts) created and configured on the respective domain, for each account in that domain, it notably contains the user name which can be used to log on that domain, the internal unique user identifier in the domain, a cryptographic hash of each user'south password for each enabled authentication protocol, the location of storage of their user registry hive, various status flags (for example if the account can be enumerated and be visible in the logon prompt screen), and the listing of domains (including the local domain) into which the account was configured.
- The "HKLM\SECURITY" fundamental usually appears empty for most users (unless they are granted access by users with administrative privileges) and is linked to the Security database of the domain into which the electric current user is logged on (if the user is logged on the local system domain, this key volition be linked to the registry hive stored past the local automobile and managed by local arrangement administrators or by the builtin "System" account and Windows installers). The kernel will access information technology to read and enforce the security policy applicative to the electric current user and all applications or operations executed by this user. It besides contains a "SAM" subkey which is dynamically linked to the SAM database of the domain onto which the electric current user is logged on.
- The "HKLM\Arrangement" key is ordinarily only writable by users with authoritative privileges on the local system. Information technology contains data about the Windows system setup, information for the secure random number generator (RNG), the list of currently mounted devices containing a filesystem, several numbered "HKLM\SYSTEM\Control Sets" containing alternative configurations for organization hardware drivers and services running on the local system (including the currently used ane and a backup), a "HKLM\SYSTEM\Select" subkey containing the status of these Command Sets, and a "HKLM\Organisation\CurrentControlSet" which is dynamically linked at boot time to the Control Set which is currently used on the local system. Each configured Command Set up contains:
- an "Enum" subkey enumerating all known Plug-and-Play devices and associating them with installed system drivers (and storing the device-specific configurations of these drivers),
- a "Services" subkey list all installed arrangement drivers (with non device-specific configuration, and the enumeration of devices for which they are instantiated) and all programs running as services (how and when they can be automatically started),
- a "Control" subkey organizing the diverse hardware drivers and programs running as services and all other system-wide configuration,
- a "Hardware Profiles" subkey enumerating the various profiles that take been tuned (each one with "Organization" or "Software" settings used to change the default profile, either in system drivers and services or in the applications) as well as the "Hardware Profiles\Electric current" subkey which is dynamically linked to one of these profiles.
- The "HKLM\SOFTWARE" subkey contains software and Windows settings (in the default hardware profile). It is mostly modified by application and arrangement installers. It is organized past software vendor (with a subkey for each), but also contains a "Windows" subkey for some settings of the Windows user interface, a "Classes" subkey containing all registered associations from file extensions, MIME types, Object Classes IDs and interfaces IDs (for OLE, COM/DCOM and ActiveX), to the installed applications or DLLs that may be handling these types on the local machine (still these associations are configurable for each user, see below), and a "Policies" subkey (also organized by vendor) for enforcing general usage policies on applications and organization services (including the primal certificates shop used for authenticating, authorizing or disallowing remote systems or services running outside the local network domain).
- The "HKLM\SOFTWARE\Wow6432Node" cardinal is used by 32-bit applications on a 64-chip Windows OS, and is equivalent to only divide from "HKLM\SOFTWARE". The key path is transparently presented to 32-bit applications by WoW64 every bit HKLM\SOFTWARE[12] (in a similar manner that 32-bit applications run across %SystemRoot%\Syswow64 as %SystemRoot%\System32)
HKEY_CLASSES_ROOT (HKCR) [edit]
- Abbreviated HKCR, HKEY_CLASSES_ROOT contains information about registered applications, such as file associations and OLE Object Form IDs, tying them to the applications used to handle these items. On Windows 2000 and above, HKCR is a compilation of user-based HKCU\Software\Classes and machine-based HKLM\Software\Classes. If a given value exists in both of the subkeys to a higher place, the one in HKCU\Software\Classes takes precedence.[13] The pattern allows for either machine- or user-specific registration of COM objects.
HKEY_USERS (HKU) [edit]
- Abbreviated HKU, HKEY_USERS contains subkeys corresponding to the HKEY_CURRENT_USER keys for each user profile actively loaded on the machine, though user hives are usually only loaded for currently logged-in users.
HKEY_CURRENT_USER (HKCU) [edit]
- Abbreviated HKCU, HKEY_CURRENT_USER stores settings that are specific to the currently logged-in user.[14] The HKEY_CURRENT_USER central is a link to the subkey of HKEY_USERS that corresponds to the user; the same information is attainable in both locations. The specific subkey referenced is "(HKU)\(SID)\..." where (SID) corresponds to the Windows SID; if the "(HKCU)" key has the following suffix "(HKCU)\Software\Classes\..." so it corresponds to "(HKU)\(SID)_CLASSES\..." i.e. the suffix has the cord "_CLASSES" is appended to the (SID).
- On Windows NT systems, each user'south settings are stored in their own files called NTUSER.DAT and USRCLASS.DAT inside their ain Documents and Settings subfolder (or their ain Users sub folder in Windows Vista and above). Settings in this hive follow users with a roaming profile from machine to automobile.
HKEY_PERFORMANCE_DATA [edit]
- This key provides runtime information into performance information provided by either the NT kernel itself, or running arrangement drivers, programs and services that provide performance data. This key is not stored in any hive and not displayed in the Registry Editor, merely it is visible through the registry functions in the Windows API, or in a simplified view via the Functioning tab of the Task Manager (only for a few operation data on the local system) or via more than advanced control panels (such as the Performances Monitor or the Performances Analyzer which allows collecting and logging these data, including from remote systems).
HKEY_DYN_DATA [edit]
- This fundamental is used but on Windows 95, Windows 98 and Windows ME.[15] Information technology contains data virtually hardware devices, including Plug and Play and network performance statistics. The information in this hive is also not stored on the difficult bulldoze. The Plug and Play information is gathered and configured at startup and is stored in retentiveness.[16]
Hives [edit]
Fifty-fifty though the registry presents itself as an integrated hierarchical database, branches of the registry are actually stored in a number of disk files chosen hives.[17] (The word hive constitutes an in-joke.)[18]
Some hives are volatile and are non stored on disk at all. An case of this is the hive of the co-operative starting at HKLM\HARDWARE. This hive records data virtually system hardware and is created each fourth dimension the arrangement boots and performs hardware detection.
Individual settings for users on a organisation are stored in a hive (disk file) per user. During user login, the system loads the user hive under the HKEY_USERS key and sets the HKCU (HKEY_CURRENT_USER) symbolic reference to indicate to the electric current user. This allows applications to store/retrieve settings for the current user implicitly under the HKCU central.
Non all hives are loaded at any i time. At boot fourth dimension, but a minimal set up of hives are loaded, and after that, hives are loaded as the operating organisation initializes and as users log in or whenever a hive is explicitly loaded by an application.
File locations [edit]
The registry is physically stored in several files, which are more often than not obfuscated from the user-mode APIs used to manipulate the data inside the registry. Depending upon the version of Windows, at that place volition be dissimilar files and dissimilar locations for these files, simply they are all on the local machine. The location for organization registry files in Windows NT is %SystemRoot%\System32\Config; the user-specific HKEY_CURRENT_USER user registry hive is stored in Ntuser.dat inside the user contour. In that location is one of these per user; if a user has a roaming profile, and then this file will be copied to and from a server at logout and login respectively. A second user-specific registry file named UsrClass.dat contains COM registry entries and does non roam by default.
Windows NT [edit]
Windows NT systems shop the registry in a binary file format which tin can be exported, loaded and unloaded by the Registry Editor in these operating systems. The following system registry files are stored in %SystemRoot%\System32\Config\:
-
Sam– HKEY_LOCAL_MACHINE\SAM -
Security– HKEY_LOCAL_MACHINE\SECURITY -
Software– HKEY_LOCAL_MACHINE\SOFTWARE -
System– HKEY_LOCAL_MACHINE\System -
Default– HKEY_USERS\.DEFAULT -
Userdiff– Not associated with a hive. Used just when upgrading operating systems.[19]
The following file is stored in each user's profile folder:
-
%USERPROFILE%\Ntuser.dat– HKEY_USERS\<User SID> (linked to by HKEY_CURRENT_USER)
For Windows 2000, Server 2003 and Windows XP, the following additional user-specific file is used for file associations and COM data:
-
%USERPROFILE%\Local Settings\Awarding Data\Microsoft\Windows\Usrclass.dat(path is localized) – HKEY_USERS\<User SID>_Classes (HKEY_CURRENT_USER\Software\Classes)
For Windows Vista and subsequently, the path was changed to:
-
%USERPROFILE%\AppData\Local\Microsoft\Windows\Usrclass.dat(path is not localized) allonym%LocalAppData%\Microsoft\Windows\Usrclass.dat– HKEY_USERS\<User SID>_Classes (HKEY_CURRENT_USER\Software\Classes)
Windows 2000 keeps an alternate copy of the registry hives (.ALT) and attempts to switch to information technology when corruption is detected.[20] Windows XP and Windows Server 2003 exercise non maintain a System.alt hive considering NTLDR on those versions of Windows can process the System.log file to bring up to appointment a System hive that has get inconsistent during a shutdown or crash. In addition, the %SystemRoot%\Repair folder contains a copy of the system'due south registry hives that were created after installation and the commencement successful startup of Windows.
Each registry data file has an associated file with a ".log" extension that acts as a transaction log that is used to ensure that any interrupted updates can exist completed upon next startup.[21] Internally, Registry files are split into four kB "bins" that contain collections of "cells".[21]
Windows 9x [edit]
The registry files are stored in the %WINDIR% directory under the names USER.DAT and SYSTEM.DAT with the addition of CLASSES.DAT in Windows ME. Also, each user contour (if profiles are enabled) has its own USER.DAT file which is located in the user's profile directory in %WINDIR%\Profiles\<Username>\.
Windows iii.11 [edit]
The only registry file is called REG.DAT and it is stored in the %WINDIR% directory.
Windows x Mobile [edit]
Annotation: To access the registry files, the Telephone needs to be set up in a special style using either:
- WpInternals ( Put the mobile device into wink manner. )
- InterOp Tools ( mountain the MainOS Partitioning with MTP. )
If whatsoever of above Methods worked - The Device Registry Files can be institute in the post-obit location:
{Telephone}\EFIESP\Windows\System32\config Notation: InterOp Tools also includes a registry editor.
Editing [edit]
Registry editors [edit]
The registry contains of import configuration information for the operating system, for installed applications as well equally individual settings for each user and awarding. A careless change to the operating system configuration in the registry could cause irreversible damage, then it is usually just installer programs which perform changes to the registry database during installation/configuration and removal. If a user wants to edit the registry manually, Microsoft recommends that a fill-in of the registry be performed before the change.[22] When a program is removed from control panel, information technology may non be completely removed and, in case of errors or glitches caused by references to missing programs, the user might accept to manually check inside directories such as program files. After this, the user might need to manually remove any reference to the uninstalled program in the registry. This is ordinarily done past using RegEdit.exe.[23] Editing the registry is sometimes necessary when working around Windows-specific issues e.grand. problems when logging onto a domain tin exist resolved by editing the registry.[24]
Windows Registry tin be edited manually using programs such equally RegEdit.exe, although these tools do not expose some of the registry's metadata such as the concluding modified engagement.
The registry editor for the 3.1/95 serial of operating systems is RegEdit.exe and for Windows NT it is RegEdt32.exe; the functionalities are merged in Windows XP. Optional and/or third-party tools similar to RegEdit.exe are available for many Windows CE versions.
Registry Editor allows users to perform the following functions:
- Creating, manipulating, renaming[25] and deleting registry keys, subkeys, values and value data
- Importing and exporting .
REGfiles, exporting information in the binary hive format - Loading, manipulating and unloading registry hive format files (Windows NT systems just)
- Setting permissions based on ACLs (Windows NT systems only)
- Bookmarking user-selected registry keys as Favorites
- Finding item strings in key names, value names and value information
- Remotely editing the registry on another networked estimator
.REG files [edit]
.REG files (as well known equally Registration entries) are text-based human-readable files for exporting and importing portions of the registry using a INI-based syntax. On Windows 2000 and later on, they contain the string Windows Registry Editor Version 5.00 at the beginning and are Unicode-based. On Windows 9x and NT 4.0 systems, they contain the string REGEDIT4 and are ANSI-based.[26] Windows 9x format .REG files are compatible with Windows 2000 and later. The Registry Editor on Windows on these systems likewise supports exporting .REG files in Windows 9x/NT format. Data is stored in .REG files using the following syntax:[26]
[<Hive proper noun>\<Key name>\<Subkey proper noun>] "Value name" = <Value type>:<Value information> The Default Value of a cardinal can exist edited past using "@" instead of "Value Name":
[<Hive proper noun>\<Fundamental proper name>\<Subkey proper noun>] @ = <Value type>:<Value information> Cord values exercise not require a <Value type> (see case), but backslashes ('\') need to be written as a double-backslash ('\\'), and quotes ('"') as backslash-quote ('\"').
For instance, to add the values "Value A", "Value B", "Value C", "Value D", "Value East", "Value F", "Value One thousand", "Value H", "Value I", "Value J", "Value K", "Value Fifty", and "Value Thousand" to the HKLM\SOFTWARE\Foobar key:
Windows Registry Editor Version 5.00 [ HKEY_LOCAL_MACHINE \SOFTWARE\Foobar] "Value A" = "<String value information with escape characters>" "Value B" = hex:<Binary data (every bit comma-delimited list of hexadecimal values)> "Value C" = dword:<DWORD value integer> "Value D" = hex(0):<REG_NONE (as comma-delimited list of hexadecimal values)> "Value E" = hex(one):<REG_SZ (as comma-delimited list of hexadecimal values representing a UTF-16LE NUL-terminated cord)> "Value F" = hex(2):<Expandable string value information (as comma-delimited list of hexadecimal values representing a UTF-16LE NUL-terminated string)> "Value Yard" = hex(3):<Binary data (every bit comma-delimited listing of hexadecimal values)> ; equal to "Value B" "Value H" = hex(4):<DWORD value (as comma-delimited list of 4 hexadecimal values, in little endian byte order)> "Value I" = hex(5):<DWORD value (as comma-delimited list of 4 hexadecimal values, in big endian byte guild)> "Value J" = hex(7):<Multi-string value data (as comma-delimited list of hexadecimal values representing UTF-16LE NUL-terminated strings)> "Value K" = hex(8):<REG_RESOURCE_LIST (as comma-delimited list of hexadecimal values)> "Value 50" = hex(a):<REG_RESOURCE_REQUIREMENTS_LIST (every bit comma-delimited list of hexadecimal values)> "Value M" = hex(b):<QWORD value (equally comma-delimited list of 8 hexadecimal values, in little endian byte society)> Data from .REG files can be added/merged with the registry past double-clicking these files or using the /s switch in the control line. REG files can also exist used to remove registry data.
To remove a cardinal (and all subkeys, values and data), the key proper name must be preceded by a minus sign ("-").[26]
For example, to remove the HKLM\SOFTWARE\Foobar key (and all subkeys, values and information),
[ - HKEY_LOCAL_MACHINE \SOFTWARE\Foobar] To remove a value (and its data), the values to be removed must have a minus sign ("-") afterward the equal sign ("=").[26]
For case, to remove simply the "Value A" and "Value B" values (and their data) from the HKLM\SOFTWARE\Foobar key:
[ HKEY_LOCAL_MACHINE \SOFTWARE\Foobar] "Value A" =- "Value B" =- To remove only the Default value of the key HKLM\SOFTWARE\Foobar (and its information):
[ HKEY_LOCAL_MACHINE \SOFTWARE\Foobar] @ =- Lines beginning with a semicolon are considered comments:
; This is a comment. This tin can be placed in any function of a .reg file [ HKEY_LOCAL_MACHINE \SOFTWARE\Foobar] "Value" = "Example string" Group policies [edit]
Windows group policies tin change registry keys for a number of machines or private users based on policies. When a policy first takes effect for a car or for an private user of a machine, the registry settings specified as part of the policy are applied to the machine or user settings.
Windows volition too look for updated policies and apply them periodically, typically every 90 minutes.[27]
Through its scope a policy defines which machines and/or users the policy is to be applied to. Whether a machine or user is inside the scope of a policy or not is defined by a gear up of rules which can filter on the location of the auto or user account in organizational directory, specific users or auto accounts or security groups. More avant-garde rules can be prepare using Windows Management Instrumentation expressions. Such rules can filter on properties such as computer vendor proper name, CPU compages, installed software, or networks connected to.
For instance, the administrator tin can create a policy with one set of registry settings for machines in the accounting department and policy with another (lock-downward) set of registry settings for kiosk terminals in the visitors area. When a machine is moved from one scope to another (e.g. changing its name or moving information technology to another organizational unit of measurement), the right policy is automatically applied. When a policy is changed it is automatically re-practical to all machines currently in its scope.
The policy is edited through a number of administrative templates which provides a user interface for picking and irresolute settings. The set of administrative templates is extensible and software packages which back up such remote assistants can register their own templates.
Command line editing [edit]
| Programmer(s) | Microsoft |
|---|---|
| Operating system | Microsoft Windows |
| Type | Command |
| License | Proprietary commercial software |
| Website | docs |
| Programmer(s) | Microsoft |
|---|---|
| Operating system | Microsoft Windows |
| Type | Command |
| License | Proprietary commercial software |
| Website | docs |
The registry tin can be manipulated in a number of means from the command line. The Reg.exe and RegIni.exe utility tools are included in Windows XP and later versions of Windows. Alternative locations for legacy versions of Windows include the Resources Kit CDs or the original Installation CD of Windows.
Also, a .REG file tin exist imported from the command line with the post-obit control:
RegEdit.exe /south file
The /s means the file will be silent merged to the registry. If the /south parameter is omitted the user will exist asked to confirm the performance. In Windows 98, Windows 95 and at least some configurations of Windows XP the /s switch also causes RegEdit.exe to ignore the setting in the registry that allows administrators to disable it. When using the /due south switch RegEdit.exe does not return an appropriate return code if the operation fails, dissimilar Reg.exe which does.
RegEdit.exe /e file
exports the whole registry in V5 format to a UNICODE .REG file, while any of
RegEdit.exe /e file HKEY_CLASSES_ROOT[\<fundamental>] RegEdit.exe /eastward file HKEY_CURRENT_CONFIG[\<primal>] RegEdit.exe /east file HKEY_CURRENT_USER[\<key>] RegEdit.exe /due east file HKEY_LOCAL_MACHINE[\<key>] RegEdit.exe /e file HKEY_USERS[\<key>]
consign the specified (sub)key (which has to be enclosed in quotes if it contains spaces) only.
RegEdit.exe /a file
exports the whole registry in V4 format to an ANSI .REG file.
RegEdit.exe /a file <cardinal>
exports the specified (sub)key (which has to be enclosed in quotes if it contains spaces) but.
Information technology is too possible to use Reg.exe. Here is a sample to display the value of the registry value Version:
Reg.exe QUERY HKLM\Software\Microsoft\ResKit /v Version Other control line options include a VBScript or JScript together with CScript, WMI or WMIC.exe and Windows PowerShell.
Registry permissions tin can exist manipulated through the command line using RegIni.exe and the SubInACL.exe tool. For case, the permissions on the HKEY_LOCAL_MACHINE\SOFTWARE key can be displayed using:
SubInACL.exe /keyreg HKEY_LOCAL_MACHINE\SOFTWARE /display PowerShell commands and scripts [edit]

Using PowerShell to navigate the registry
Windows PowerShell comes with a registry provider which presents the registry as a location type like to the file organization. The same commands used to dispense files and directories in the file system tin be used to dispense keys and values of the registry.[28]
As well similar the file system, PowerShell uses the concept of a current location which defines the context on which commands by default operate. The Get-ChildItem (too available through the aliases ls, dir or gci) retrieves the child keys of the current location. By using the Set-Location (or the allonym cd) control the user tin change the electric current location to another key of the registry.[28] Commands which rename items, remove items, create new items or set content of items or properties can be used to rename keys, remove keys or entire sub-trees or change values.
Through PowerShell scripts files, an ambassador can prepare scripts which, when executed, make changes to the registry. Such scripts can be distributed to administrators who can execute them on individual machines. The PowerShell Registry provider supports transactions, i.eastward. multiple changes to the registry tin be bundled into a single atomic transaction. An atomic transaction ensures that either all of the changes are committed to the database, or if the script fails, none of the changes are committed to the database.[28] [29]
Programs or scripts [edit]
The registry can be edited through the APIs of the Advanced Windows 32 Base API Library (advapi32.dll).[30]
Many programming languages offer built-in runtime library functions or classes that wrap the underlying Windows APIs and thereby enable programs to store settings in the registry (e.g. Microsoft.Win32.Registry in VB.NET and C#, or TRegistry in Delphi and Free Pascal). COM-enabled applications similar Visual Bones 6 tin apply the WSH WScript.Shell object. Some other way is to utilize the Windows Resource Kit Tool, Reg.exe by executing it from code,[31] although this is considered poor programming do.
Similarly, scripting languages such every bit Perl (with Win32::TieRegistry), Python (with winreg), TCL (which comes bundled with the registry package),[32] Windows Powershell and Windows Scripting Host as well enable registry editing from scripts.
Offline editing [edit]
The offreg.dll[33] available from the Windows Driver Kit offers a gear up of APIs for the creation and manipulation of currently not loaded registry hives similar to those provided by advapi32.dll.
It is also possible to edit the registry (hives) of an offline arrangement from Windows PE or Linux (in the latter case using open source tools).
COM self-registration [edit]
Prior to the introduction of registration-complimentary COM, developers were encouraged to add initialization lawmaking to in-process and out-of-process binaries to perform the registry configuration required for that object to work. For in-process binaries such as .DLL and .OCX files, the modules typically exported a function called DllInstall()[34] that could exist called past installation programs or invoked manually with utilities like Regsvr32.exe;[35] out-of-process binaries typically support the commandline arguments /Regserver and /Unregserver that created or deleted the required registry settings.[36] COM applications that break because of DLL Hell problems tin normally exist repaired with RegSvr32.exe or the /RegServer switch without having to re-invoke installation programs.[37]
Avant-garde functionality [edit]
Windows exposes APIs that allows user-way applications to register to receive a notification event if a detail registry key is changed.[38] APIs are likewise available to let kernel-mode applications to filter and modify registry calls made by other applications.[39]
Windows also supports remote access to the registry of another computer via the RegConnectRegistry role[forty] if the Remote Registry service is running, correctly configured and its network traffic is not firewalled.[41]
Security [edit]
Each key in the registry of Windows NT versions tin can take an associated security descriptor. The security descriptor contains an access control list (ACL) that describes which user groups or individual users are granted or denied access permissions. The set of registry permissions include x rights/permissions which can be explicitly allowed or denied to a user or a group of users.
| Permission | Description |
|---|---|
| Query Value | The right to read the registry cardinal value. |
| Set Value | The correct to write a new value |
| Create Subkey | The right to create subkeys. |
| Enumerate Subkeys | Allow the enumeration of subkeys. |
| Notify | The right to request change notifications for registry keys or subkeys. |
| Create Link | Reserved by the operating system. |
| Delete | The right to delete a key. |
| Write DACL | The right to modify permissions of the container'southward DACL. |
| Write Owner | The correct to modify the container'due south possessor. |
| Read Control | The right to read the DACL. |
Every bit with other securable objects in the operating system, private access command entries (ACE) on the security descriptor can be explicit or inherited from a parent object.[42]
Windows Resource Protection is a characteristic of Windows Vista and later versions of Windows that uses security to deny Administrators and the organisation WRITE admission to some sensitive keys to protect the integrity of the system from malware and accidental modification.[43]
Special ACEs on the security descriptor tin can also implement mandatory integrity control for the registry primal and subkeys. A procedure running at a lower integrity level cannot write, change or delete a registry key/value, even if the account of the process has otherwise been granted admission through the ACL. For instance, Internet Explorer running in Protected Mode can read medium and low integrity registry keys/values of the currently logged on user, but it can only change low integrity keys.[44]
Outside security, registry keys cannot be deleted or edited due to other causes. Registry keys containing NUL characters cannot be deleted with standard registry editors and require a special utility for deletion, such every bit RegDelNull.[45] [46]
Backups and recovery [edit]
Dissimilar editions of Windows take supported a number of dissimilar methods to back upwards and restore the registry over the years, some of which are now deprecated:
- System Restore can back upwardly the registry and restore it as long as Windows is bootable, or from the Windows Recovery Environment (starting with Windows Vista).
- NTBackup tin can back upwardly the registry as part of the Arrangement State and restore information technology. Automatic System Recovery in Windows XP tin can as well restore the registry.
- On Windows NT, the Last Known Good Configuration option in startup carte du jour relinks the
HKLM\Arrangement\CurrentControlSetkey, which stores hardware and device commuter data. - Windows 98 and Windows ME include command line (Scanreg.exe) and GUI (Scanregw.exe) registry checker tools to check and set up the integrity of the registry, create up to v automatic regular backups by default and restore them manually or whenever corruption is detected.[47] The registry checker tool backs up the registry, by default, to
%Windir%\SysbckupScanreg.exe tin as well run from MS-DOS.[48] - The Windows 95 CD-ROM included an Emergency Recovery Utility (ERU.exe) and a Configuration Fill-in Tool (Cfgback.exe) to back up and restore the registry. Additionally Windows 95 backs upwards the registry to the files organisation.da0 and user.da0 on every successful boot.
- Windows NT iv.0 included
RDISK.EXE, a utility to support and restore the entire registry.[49] - Windows 2000 Resource Kit contained an unsupported pair of utilities called Regback.exe and RegRest.exe for backup and recovery of the registry.[l]
- Periodic automatic backups of the registry are now disabled by default on Windows 10 May 2019 Update (version 1903). Microsoft recommends System Restore be used instead.[51]
Policy [edit]
Grouping policy [edit]
Windows 2000 and afterwards versions of Windows use Group Policy to enforce registry settings through a registry-specific client extension in the Group Policy processing engine.[52] Policy may be applied locally to a single computer using gpedit.msc, or to multiple users and/or computers in a domain using gpmc.msc.
Legacy systems [edit]
With Windows 95, Windows 98, Windows ME and Windows NT 4.0, administrators can use a special file to be merged into the registry, called a policy file (POLICY.POL). The policy file allows administrators to preclude non-administrator users from irresolute registry settings similar, for case, the security level of Internet Explorer and the desktop background wallpaper. The policy file is primarily used in a business with a large number of computers where the business needs to be protected from rogue or careless users.
The default extension for the policy file is .Politico. The policy file filters the settings information technology enforces by user and past group (a "group" is a defined ready of users). To practise that the policy file merges into the registry, preventing users from circumventing it past simply irresolute back the settings. The policy file is usually distributed through a LAN, simply can be placed on the local computer.
The policy file is created by a free tool by Microsoft that goes by the filename poledit.exe for Windows 95/Windows 98 and with a computer management module for Windows NT. The editor requires authoritative permissions to be run on systems that uses permissions. The editor can also directly change the electric current registry settings of the local computer and if the remote registry service is installed and started on another estimator it can likewise change the registry on that computer. The policy editor loads the settings it tin modify from .ADM files, of which one is included, that contains the settings the Windows shell provides. The .ADM file is patently text and supports piece of cake localisation by allowing all the strings to exist stored in ane place.
Virtualization [edit]
INI file virtualization [edit]
Windows NT kernels support redirection of INI file-related APIs into a virtual file in a registry location such as HKEY_CURRENT_USER using a feature chosen "InifileMapping".[53] This functionality was introduced to allow legacy applications written for 16-bit versions of Windows to be able to run under Windows NT platforms on which the System folder is no longer considered an appropriate location for user-specific data or configuration. Not-compliant 32-bit applications can also be redirected in this fashion, even though the feature was originally intended for 16-fleck applications.
Registry virtualization [edit]
Windows Vista introduced limited registry virtualization, whereby poorly written applications that do non respect the principle of to the lowest degree privilege and instead endeavour to write user data to a read-only organization location (such every bit the HKEY_LOCAL_MACHINE hive), are silently redirected to a more appropriate location, without irresolute the awarding itself.
Similarly, application virtualization redirects all of an application's invalid registry operations to a location such as a file. Used together with file virtualization, this allows applications to run on a auto without being installed on it.
Low integrity processes may also use registry virtualization. For example, Cyberspace Explorer 7 or viii running in "Protected Fashion" on Windows Vista and higher up will automatically redirect registry writes by ActiveX controls to a sandboxed location in order to frustrate some classes of security exploits.
The Application Compatibility Toolkit[54] provides shims that tin can transparently redirect HKEY_LOCAL_MACHINE or HKEY_CLASSES_ROOT Registry operations to HKEY_CURRENT_USER to accost "LUA" bugs that cause applications not to work for users with bereft rights.
Disadvantages [edit]
Critics labeled the registry in Windows 95 a single betoken of failure, considering re-installation of the operating system was required if the registry became corrupt.[ citation needed ] However, Windows NT uses transaction logs to protect against abuse during updates. Current versions of Windows use 2 levels of log files to ensure integrity even in the instance of power failure or like catastrophic events during database updates.[55] Even in the example of a non-recoverable error, Windows tin repair or re-initialize damaged registry entries during organization boot.[55]
Equivalents and alternatives [edit]
In Windows, employ of the registry for storing program information is a affair of developer's discretion. Microsoft provides programming interfaces for storing data in XML files (via MSXML) or database files (via SQL Server Meaty) which developers can use instead. Developers are also free to use non-Microsoft alternatives or develop their own proprietary data stores.
In contrast to Windows Registry's binary-based database model, some other operating systems use separate plain-text files for daemon and application configuration, but group these configurations together for ease of management.
- In Unix-similar operating systems (including Linux) that follow the Filesystem Hierarchy Standard, system-wide configuration files (information similar to what would appear in HKEY_LOCAL_MACHINE on Windows) are traditionally stored in files in
/etc/and its subdirectories, or sometimes in/usr/local/etc. Per-user information (information that would be roughly equivalent to that in HKEY_CURRENT_USER) is stored in hidden directories and files (that start with a period/total cease) inside the user's home directory. However XDG-compliant applications should refer to the environment variables divers in the Base Directory specification.[56] - In macOS, organisation-wide configuration files are typically stored in the
/Library/binder, whereas per-user configuration files are stored in the corresponding~/Library/folder in the user's home directory, and configuration files set up past the system are in/System/Library/. Within these respective directories, an application typically stores a belongings list file in thePreferences/sub-directory. - RISC OS (not to be confused with MIPS RISC/bone) uses directories for configuration information, which allows applications to be copied into awarding directories, as opposed to the separate installation process that typifies Windows applications; this arroyo is also used on the ROX Desktop for Linux.[57] This directory-based configuration likewise makes it possible to apply unlike versions of the aforementioned application, since the configuration is done "on the wing".[58] If one wishes to remove the application, it is possible to but delete the folder belonging to the application.[59] [60] This will often not remove configuration settings which are stored independently from the application, usually inside the calculator'southward !Boot construction, in !Boot.Choices or potentially anywhere on a network fileserver. It is possible to re-create installed programs between computers running RISC Bone by copying the application directories belonging to the programs, however some programs may require re-installing, e.g. when shared files are placed outside an application directory.[58]
- IBM AIX (a Unix variant) uses a registry component chosen Object Data Manager (ODM). The ODM is used to shop information about system and device configuration. An extensive fix of tools and utilities provides users with means of extending, checking, correcting the ODM database. The ODM stores its information in several files, default location is
/etc/objrepos. - The GNOME desktop environment uses a registry-similar interface called dconf for storing configuration settings for the desktop and applications.
- The Elektra Initiative provides alternative back-ends for various different text configuration files.
- While not an operating system, the Wine compatibility layer, which allows Windows software to run on a Unix-like system, too employs a Windows-like registry as text files in the WINEPREFIX folder: system.reg (HKEY_LOCAL_MACHINE), user.reg (HKEY_CURRENT_USER) and userdef.reg.[61]
See too [edit]
- Registry cleaner
- Application virtualization
- LogParser – SQL-like querying of various types of log files
- List of Trounce Icon Overlay Identifiers
- Ransomware attack that uses Registry
Notes [edit]
- ^ When applications fail to execute considering they request more than privileges than they require (and are denied those privileges), this is known as a limited user awarding (LUA) issues.
Footnotes [edit]
- ^ Esposito, Dino (November 2000). "Windows 2000 Registry: Latest Features and APIs Provide the Power to Customize and Extend Your Apps". MSDN Magazine. Microsoft. Archived from the original on April fifteen, 2003. Retrieved July 19, 2007.
- ^ a b c "The Arrangement Registry".
- ^ "Windows 95 Compages Components". www.microsoft.com. Archived from the original on Feb vii, 2008. Retrieved Apr 29, 2008.
The following table shows other difficulties or limitations caused past using .INI files that are overcome past using the Registry.
- ^ Hipson 2002, p. 5, 41–43.
- ^ Richter, Jeffrey; Nasarre, Christophe (2008). Windows Via C/C++ (5th ed.). Microsoft Press. ISBN9780735642461 . Retrieved August 28, 2021.
- ^ Raymond Chen, "Why do registry keys take a default value?"
- ^ Hipson 2002, pp. 207, 513–514.
- ^ Hipson 2002, pp. 520–521.
- ^ Hipson 2002, p. seven.
- ^ "Designed for Windows XP Application Specification". Microsoft. August 20, 2002. Retrieved Apr 8, 2009.
- ^ "HKEY_LOCAL_MACHINE". Gautam. 2009. Retrieved April 8, 2009.
- ^ "Registry Keys Affected by WOW64 (Windows)". Msdn.microsoft.com. Retrieved April 10, 2014.
- ^ "Description of the Microsoft Windows registry". Retrieved September 25, 2008.
- ^ "HKEY_CURRENT_USER". Microsoft. 2009. Retrieved April 8, 2009.
- ^ "Clarification of the HKEY_DYN_DATA Registry Key in Windows 95, Windows 98, and Windows 98 SE". support.microsoft.com.
- ^ "A Closer Look at HKEY_DYN_DATA". rinet.ru. Archived from the original on May nine, 2008.
- ^ "Registry hives". Retrieved July 19, 2007.
- ^ Chen, Raymond (August 8, 2011). "Why is a registry file called a "hive"?". The Old New Affair. Retrieved July 29, 2011.
- ^ "Overview of the Windows NT Registry". Retrieved December 2, 2011.
- ^ "Inside the Registry". Retrieved Dec 28, 2007.
- ^ a b Norris, Peter (February 2009). "The Internal Structure of the Windows Registry" (PDF). Cranfield Academy. Archived from the original (PDF) on May 29, 2009.
- ^ "Incorrect Icons Displayed for .ico Files". November fifteen, 2009. Retrieved March 31, 2012.
- ^ "How to Completely Uninstall / Remove a Software Program in Windows without using 3rd Party Software? - AskVG". www.askvg.com.
- ^ "Y'all may receive a "Cease 0x00000035 NO_MORE_IRP_STACK_LOCATIONS" mistake message when you try to log on to a domain". October nine, 2011. Retrieved March 31, 2012. This page tells the user to edit the registry when resolving the result.
- ^ key renaming is implemented every bit removal and add while retaining subkeys/values, as the underlying APIs do not support the rename part directly
- ^ a b c d "How to add, alter, or delete registry subkeys and values past using a .reg file". support.microsoft.com.
- ^ "Applying Group Policy". Microsoft.
- ^ a b c Payette, Bruce; Siddaway, Richard (2018). Windows PowerShell in Action (Tertiary ed.). Manning Publications. pp. 7–8, 24, 608, 708–710. ISBN9781633430297 . Retrieved August 28, 2021.
- ^ Warner, Timothy L. (May 2015). Windows PowerShell in 24 Hours, Sams Teach Yourself. Sams Publishing. p. nineteen, 211. ISBN9780134049359 . Retrieved August 28, 2021.
- ^ "Reading and Writing Registry Values with Visual Bones". Retrieved July 19, 2007.
- ^ "REG command in Windows XP". Retrieved July nineteen, 2007.
- ^ "registry manual folio – Tcl Bundled Packages". world wide web.tcl.tk . Retrieved December 14, 2017.
- ^ "Offline Registry Library". Retrieved June 4, 2014.
- ^ "DllInstall Function". Microsoft. March seven, 2012. Retrieved March 22, 2012.
- ^ "Regsvr32". Microsoft. Retrieved March 22, 2012.
- ^ "How to: Annals Automation Servers". Microsoft. Retrieved March 22, 2012.
- ^ "How to re-register PowerPoint 2000, PowerPoint 2003, PowerPoint 2007 and PowerPoint 2010". Microsoft. January 2012. Retrieved March 22, 2012.
- ^ "RegNotifyChangeKeyValue function". Microsoft.
- ^ "Registering for Notifications". Microsoft.
- ^ "RegConnectRegistry function". Microsoft.
- ^ "How to Manage Remote Access to the Registry". Microsoft.
- ^ Gibson, Darril (June 28, 2011). "Chapter 4: Securing Admission with Permissions". Microsoft Windows security : essentials. Indianapolis, Ind.: Wiley. ISBN978-ane-118-01684-viii.
- ^ "Application Compatibility: Windows Resource Protection (WRP)". Microsoft. Retrieved August 8, 2012.
- ^ Marc Silbey, Peter Brundrett. "Understanding and Working in Protected Mode Internet Explorer". Retrieved Baronial 8, 2012.
- ^ "RegDelNull v1.1". November i, 2006. Retrieved August 8, 2012.
- ^ "Unable to delete certain registry keys – Mistake while deleting key". March 23, 2010. Retrieved August 8, 2012. Microsoft Back up folio.
- ^ "Description of the Windows Registry Checker Tool (Scanreg.exe)".
- ^ "Command-Line Switches for the Registry Checker Tool".
- ^ "How To Fill-in, Edit, and Restore the Registry in Windows NT iv.0". support.microsoft.com.
- ^ "Technical Reference to the Registry: Related Resources". Microsoft. Retrieved September 9, 2011.
- ^ "Microsoft Kills Automatic Registry Backups in Windows 10". ExtremeTech . Retrieved July 1, 2019.
- ^ "How Cadre Group Policy Works". Microsoft. September two, 2009. Retrieved August 13, 2012.
- ^ "Chapter 26 – Initialization Files and the Registry". Microsoft. Retrieved March 3, 2008.
- ^ "Microsoft Application Compatibility Toolkit 5.0". Microsoft. Retrieved July 26, 2008.
- ^ a b Ionescu, Marker Russinovich, David A. Solomon, Alex (2012). "Registry Internals". Windows internals (6th ed.). Redmond, Launder.: Microsoft Press. ISBN978-0-7356-4873-9.
- ^ "XDG Base Directory Specification". standards.freedesktop.org.
- ^ "Awarding directories". Archived from the original on May 27, 2012. Retrieved May 17, 2012.
- ^ a b "Example Studies Of The Top 132 Annoyances With Operating Systems Other Than RISC Os". Retrieved April 3, 2012. Page from the riscos.com website. Mentioned in points 82 and 104.
- ^ "RISC Bone tour". Retrieved July nineteen, 2007.
- ^ "The RISC Bone Products Directory". November 2, 2006. Archived from the original on Feb xix, 2007. Retrieved April ane, 2012.
- ^ 3.2. Using the Registry and Regedit (Wine User Guide)
References [edit]
- Hipson, Peter (2002). Mastering Windows XP Registry. Wiley. ISBN0-7821-2987-0 . Retrieved August 28, 2021.
- Russinovich, Marker East.; Solomon, David A. (2005). Microsoft Windows Internals (Fourth ed.). Microsoft Printing. pp. 183–236. ISBN978-0-7356-1917-three.
External links [edit]
- Windows Registry info & reference in the MSDN Library
Source: https://en.wikipedia.org/wiki/Windows_Registry
Posted by: langstonbillostrand.blogspot.com


0 Response to "When A User Makes Changes To The Settings Of A Windows System, Where Are These Changes Stored?"
Post a Comment